Booting Ubuntu on Google Chromecast With Google TV
Posted on Mon 29 November 2021 in Article • Tagged with arm, amlogic, bootloader, bootrom, chromecast, uboot, ubuntu, usb
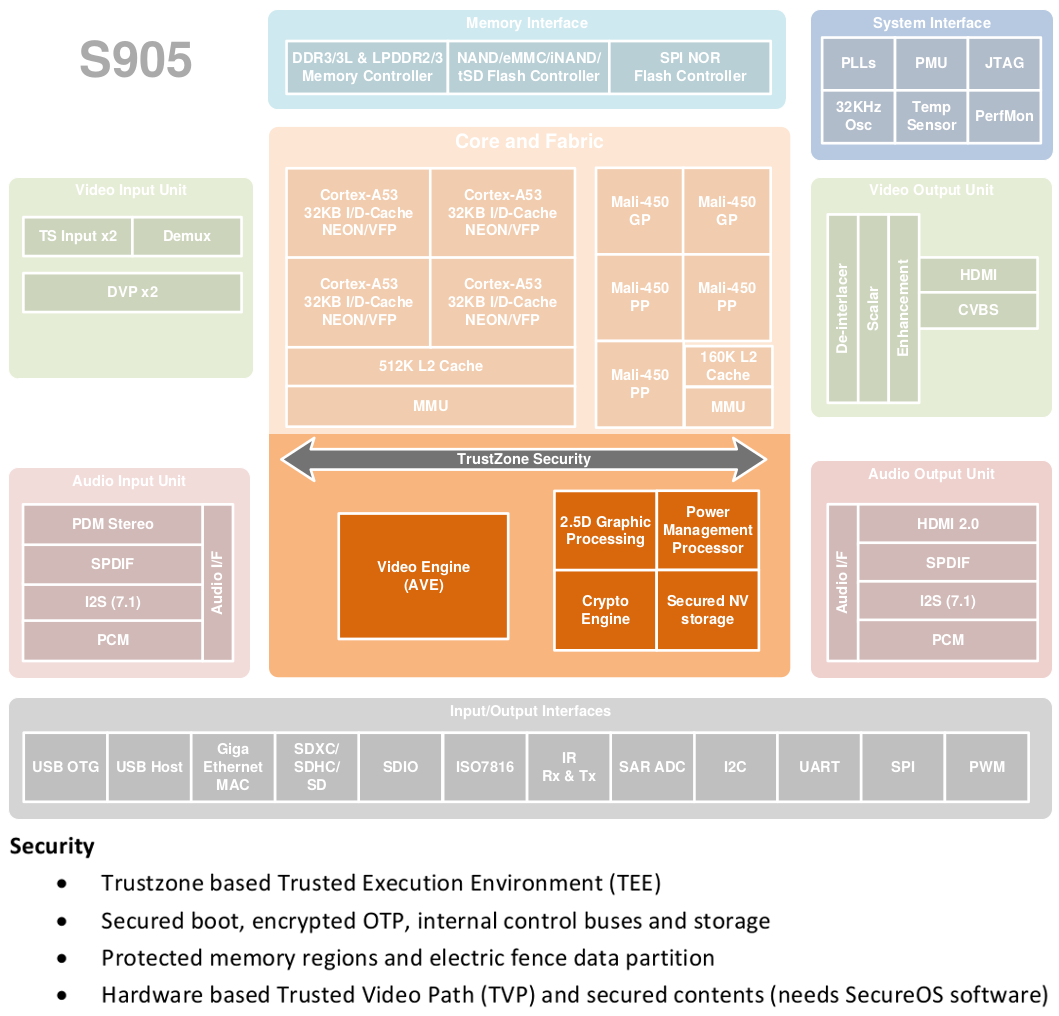
In a previous post, we detailed a vulnerability in the Amlogic System-On-Chip bootROM that allows arbitrary code execution at EL3. Since the Chromecast with Google TV (CCwGTV) is one of the devices affected by this issue, it opens the possibility to run a custom OS like Ubuntu.
This post describes …
Continue reading